Identify your Risks in Real-time with
Automated Network Penetration Testing
Deploy. Click. Go.
Hello World, Meet
The industry’s most valued automated network penetration testing platform.
- Perform an internal or external network penetration test whenever you want, however often you want.
- More extensive and goes way beyond an automated vulnerability scan.
- Over 60% less than the cost of a traditional or manual network penetration test.
- Real-time monitoring of network penetration test and progress.
- The entire solution meets compliance requirements for regulated industries: PCI, HIPAA, SOC2, etc., and cyber insurance.
- Backed by OSCP and OSCE certified consultants with 10+ years experience.
Test Your Defenses
See what a hacker sees on your network before they do.
vPenTest is essentially a hacker on a company’s network. It looks for sensitive data, performs exploits, conducts man-in-the-middle attacks, crack password hashes, escalates privileges on the network, and even impersonates users to find sensitive data. It goes beyond identifying vulnerabilities by actually exploiting them to demonstrate what happens if an attacker got access to the network.
Our Modern Approach to PenTesting
We make network penetration testing easy, efficient, scalable, and affordable for businesses that take cyber security seriously.
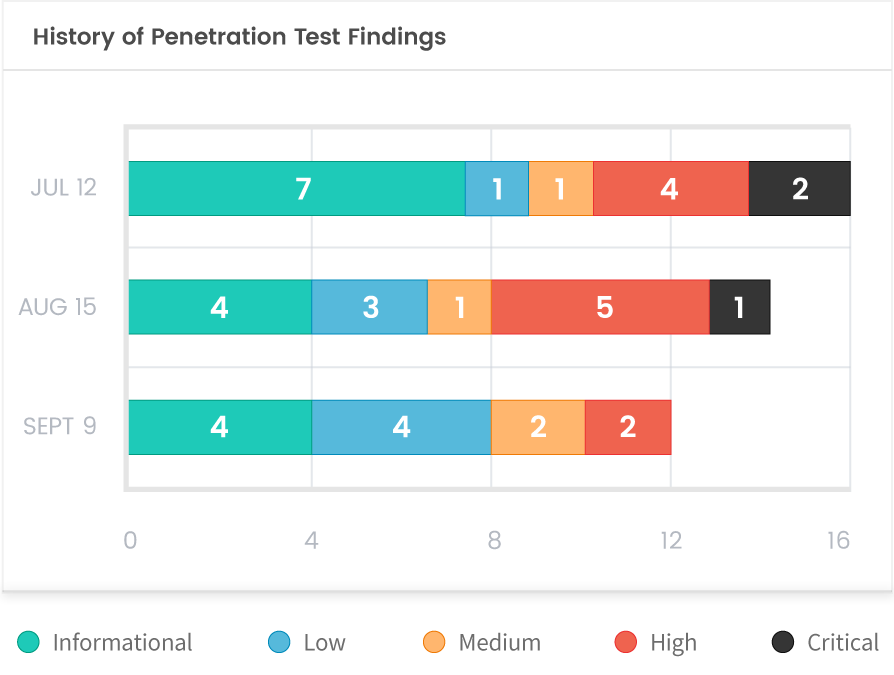
Continuous
Test your network monthly or as new threats emerge. Schedule a test within minutes and keep track of your organization’s risk profile in near real-time. Our reports will show you trending data, allowing your team to see improvements from one month to another.
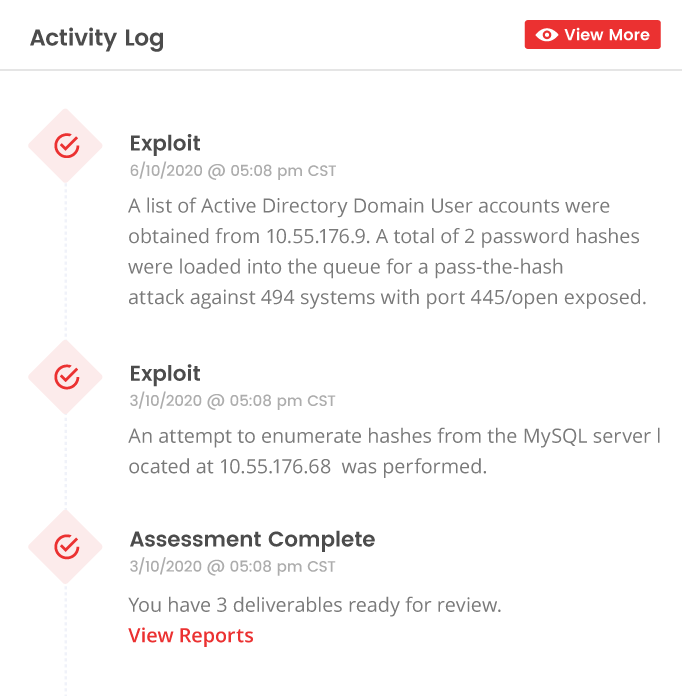
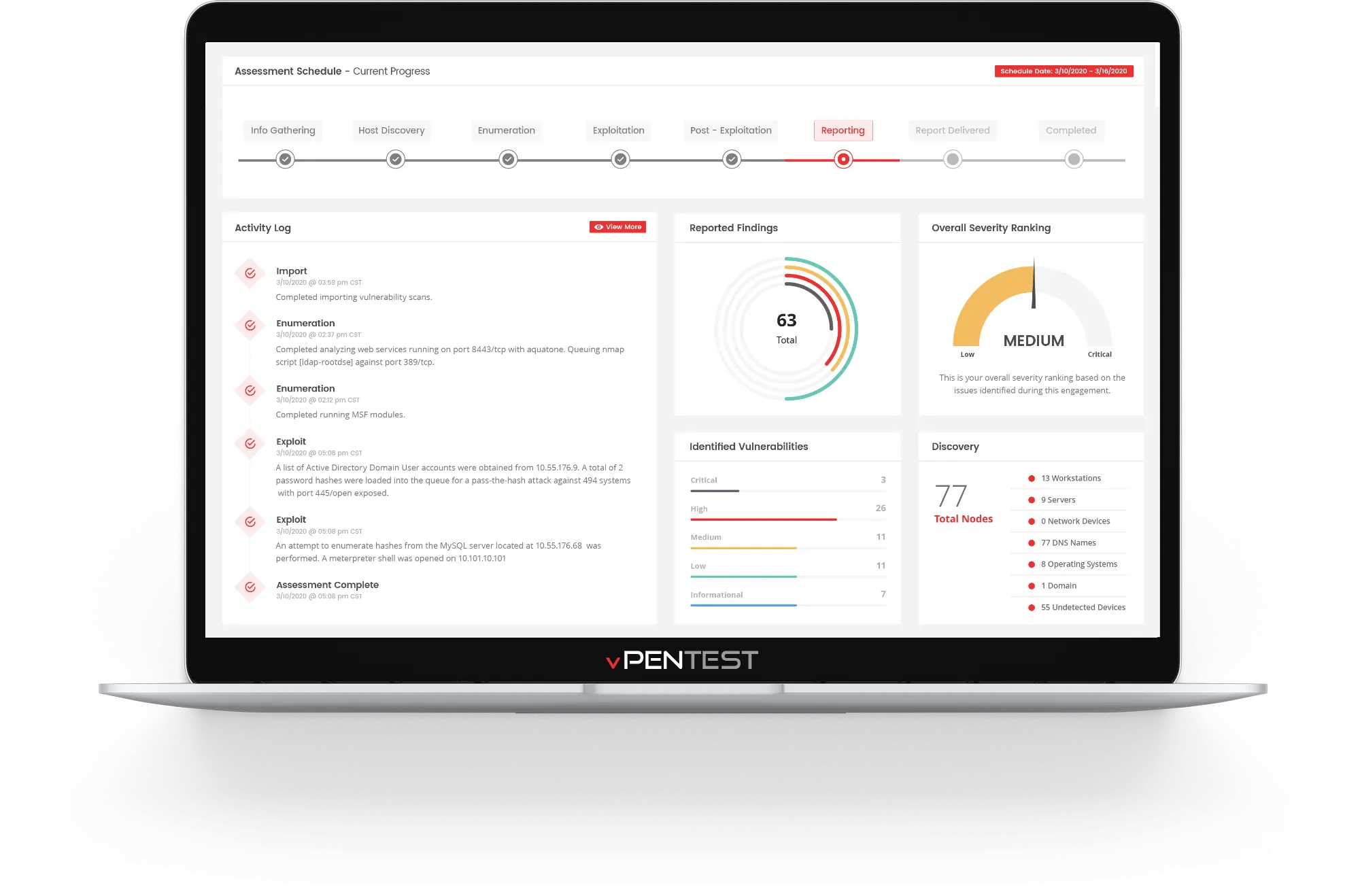
Real-time Visibility
Correlate our Activity Log with your SIEM and incident response procedures. Our real-time activity logs ensures your organization knows what’s happening and when. Find gaps in your security monitoring controls as the network penetration test occurs in real-time.
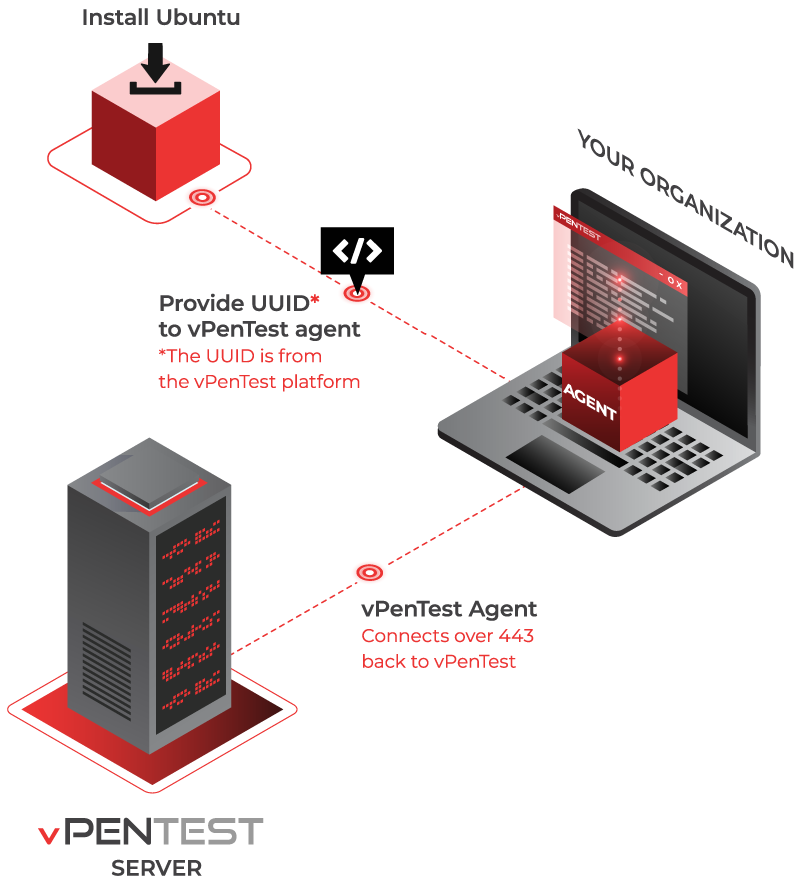
Save Time & Be in Control
Deploy an agent, schedule an internal assessment, and get detailed reports within a few days. You’re in command. You control the schedule, frequency, and scope of every assessment. Simply deploy, click and go.
Red Team on Demand
Take advantage of the expertise of seasoned penetration testers without hiring one.
vPenTest is equivalent to hiring a team of eCPPT, OSCP, and OSCE certified consultants with decades of experience and over 13 industry certifications to help you carry out a network penetration test with the click of a few buttons. Be Secure. Be Fast. Be the Hacker.

Quality Reports to Share With the Team
vPenTest generates a report for you and your team to review within 48 hours after the penetration test is complete.
A Few Bytes From Our Partners
OUR LATEST RESOURCES
At Vonahi Security, we are constantly building new ways to strengthen your defenses. Follow #vonahisec to stay ahead of the game.
FREE RESOURCES
ANNOUNCEMENT / BLOG
Hackers Don't Sleep. Neither Does vPenTest.
If your organization was targeted tomorrow, would you be prepared? Let's work together and find out.